XVC768117 3BHB007211R117 ABB 工控模块 瑞士

工业公司应确保自身网络设计良好,有着防护周全的边界。企业应按ISA IEC 62443标准划分自身网络,保护所有无线应用,部署能快速排除故障的安全远程访问解决方案。公司网络,包括其工业网络基础设施设备,都应列入监视对象范围。运营技术(OT)团队可能会觉得公司的终端受到边界防火墙、专利安防软件、专业协议和物理隔离的防护,可以抵御数字攻击。但事实不是这样的,雇员、承包商和供应链员工将他们的笔记本电脑或U盘带入企业网络时,这些安全防护措施就被绕过了。必须确保所有终端都是安全的,要防止员工将自己的设备接入公司网络。事实上,黑客可以侵入OT环境中基于PC的终端。公司企业还应保护其IT终端不受OT环境中横向移动的数字攻击侵袭。
XVC768117 3BHB007211R117 ABB 工控模块 瑞士
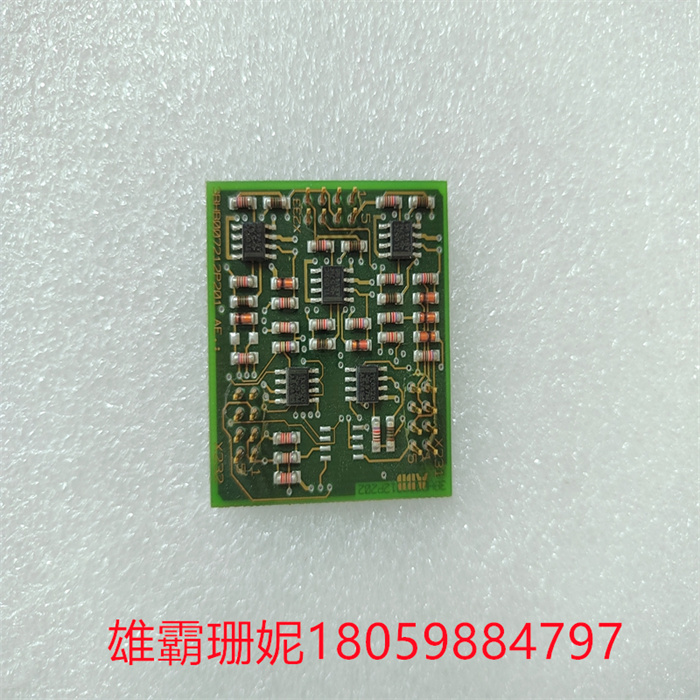
An electronic device capable of controlling voltage and/or current to generate gain, oscillation or similar integration functions. It consists of a series of electronic components, such as capacitors, resistors, coils, relays, transistors, semiconductor devices and microcircuits, which are all packed in a replaceable package. The configuration, physical dimensions and electrical parameters of the project have been standardized according to government and/or industry norms and/or standards. Excluding items with non-standardized configuration. Unlike circuit card assemblies and electronic component assemblies, it does not need to be disassembled.
XVC768117 3BHB007211R117 ABB 工控模块 瑞士

Industrial companies should ensure that their networks are well designed and have well-protected borders. Enterprises should divide their own networks according to ISA IEC 62443 standard, protect all wireless applications, and deploy secure remote access solutions that can quickly troubleshoot. The company network, including its industrial network infrastructure equipment, should be included in the scope of monitoring. Operational Technology (OT) teams may feel that the company's terminals are protected by border firewalls, proprietary security software, professional protocols and physical isolation, and can resist digital attacks. But this is not the case. When employees, contractors and supply chain employees bring their laptops or USB flash drives into the enterprise network, these security measures are bypassed. All terminals must be secure, and employees should be prevented from connecting their devices to the company network. In fact, hackers can invade PC-based terminals in the OT environment. Companies should also protect their IT terminals from digital attacks that move horizontally in the OT environment.

Copyright © 2022-2024 厦门雄霸电子商务有限公司 版权所有 备案号:闽ICP备14012685号-33